Security
What is clickjacking and how can you prevent it?

Attackers use what is called an Inline Frame (iFrame) that loads another HTML page within the original website. That iFrame generally imitates the original website, making the user think they are still operating on the original website. The root of this problem is a function that allows a website to load content and scripts from another website.
Configuring X-Frame-options prevents abuse
A website owner can prevent this by configuring the X-Frame-Options in the HTTP header of their website. The X-Frame-Options HTTP header can be used to indicate whether a browser should be allowed to render a page in a <frame>, <iframe>, <embed> or <object>. This solution can prevent clickjacking attacks by ensuring that foreign content isn’t embedded into the website.
This doesn't mean websites can’t embed content from other websites, you just need to specify who can load content on your website in the header: for example, you can allow specific content from Instagram.
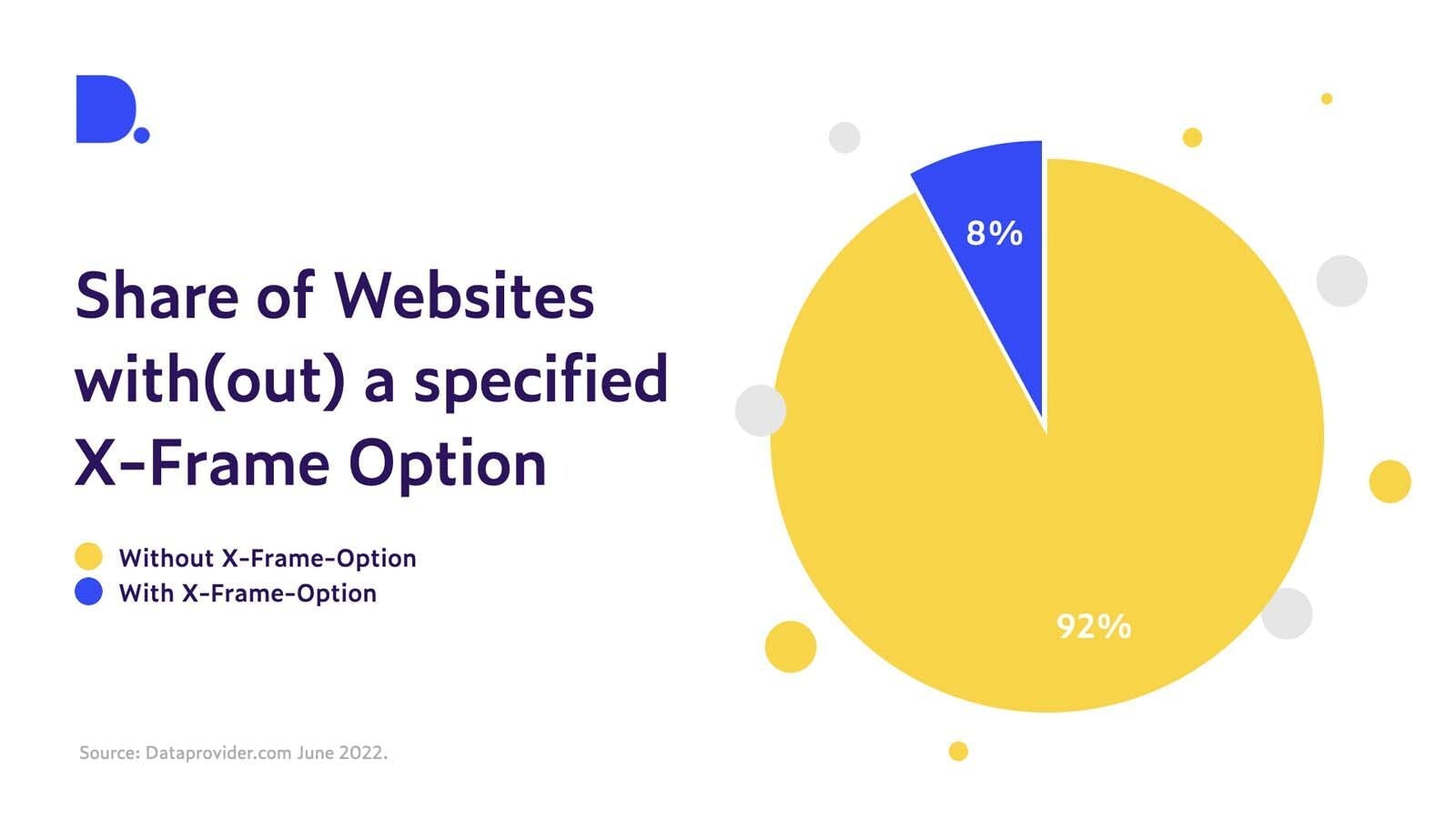
Implementing X-Frame-Options isn’t hard. Yet, when we look at our data, we see that only a tiny proportion of websites globally have implemented an X-Frame-Option in their HTTP header. Out of the more than 120 million websites scanned for this research, only 8% (9.5 million) are protected against clickjacking.
This is staggeringly low. Given the ever-increasing threat of cyberattacks, preventing clickjacking from happening by implementing an X-Frame-Option is a simple way to make the web just a bit safer for everyone.
Preventing clickjacking from happening by implementing an X-Frame-Option is a simple way to make the web just a little bit safer for everyone.