Security
Security.txt: the web's unsung guardian

Security.txt is an internet draft standard for websites to define their security policies. It’s a simple text file that provides the necessary contact information for security researchers to report vulnerabilities they’ve discovered on your website. Yet, it's surprising how few organizations are taking advantage of this convenient cybersecurity tool.
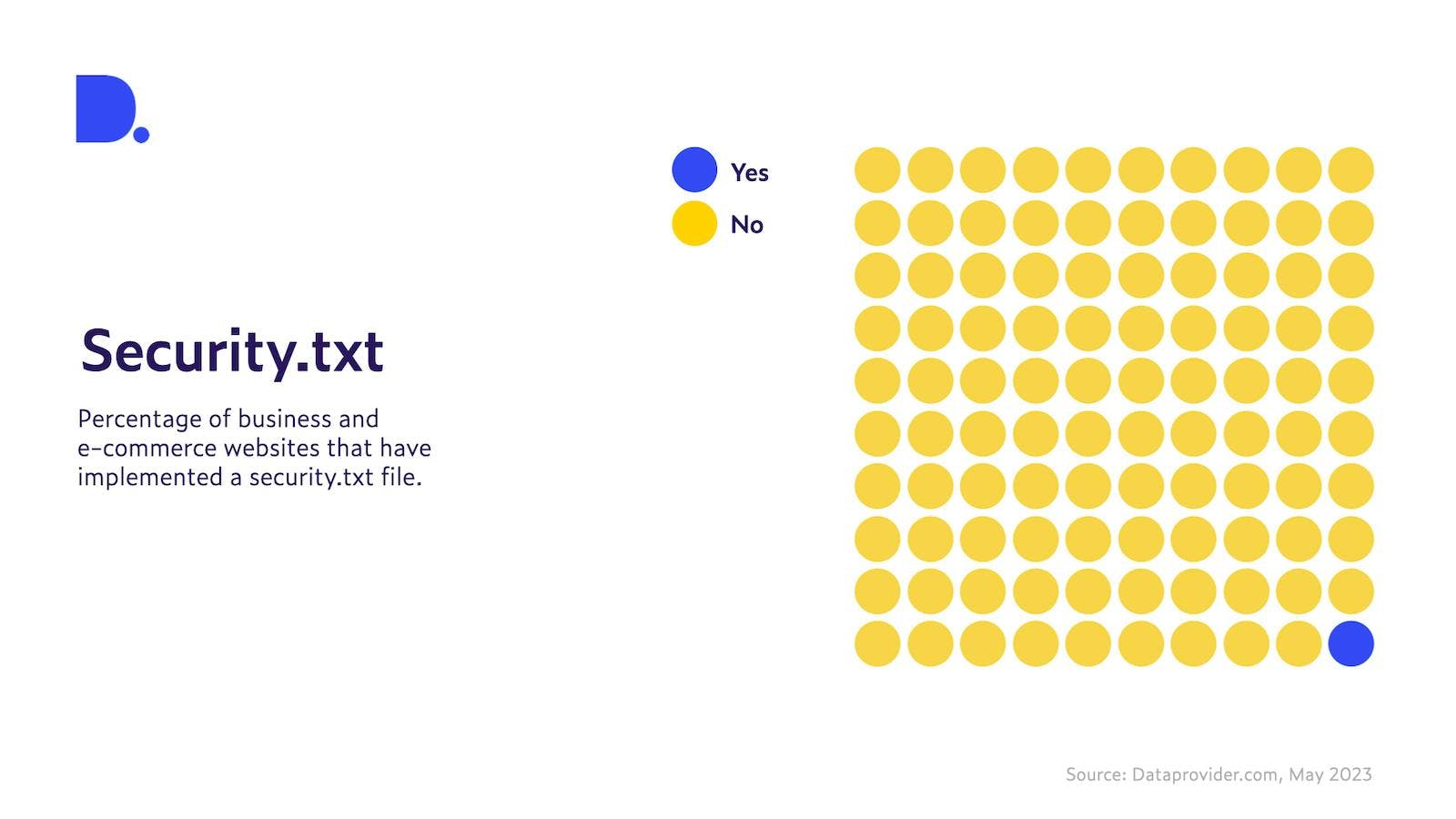
We looked at 38.7 million business and e-commerce websites globally. Among these, only 209,000 have a security.txt file implemented. That is less than 1% of the total (Figure 1).
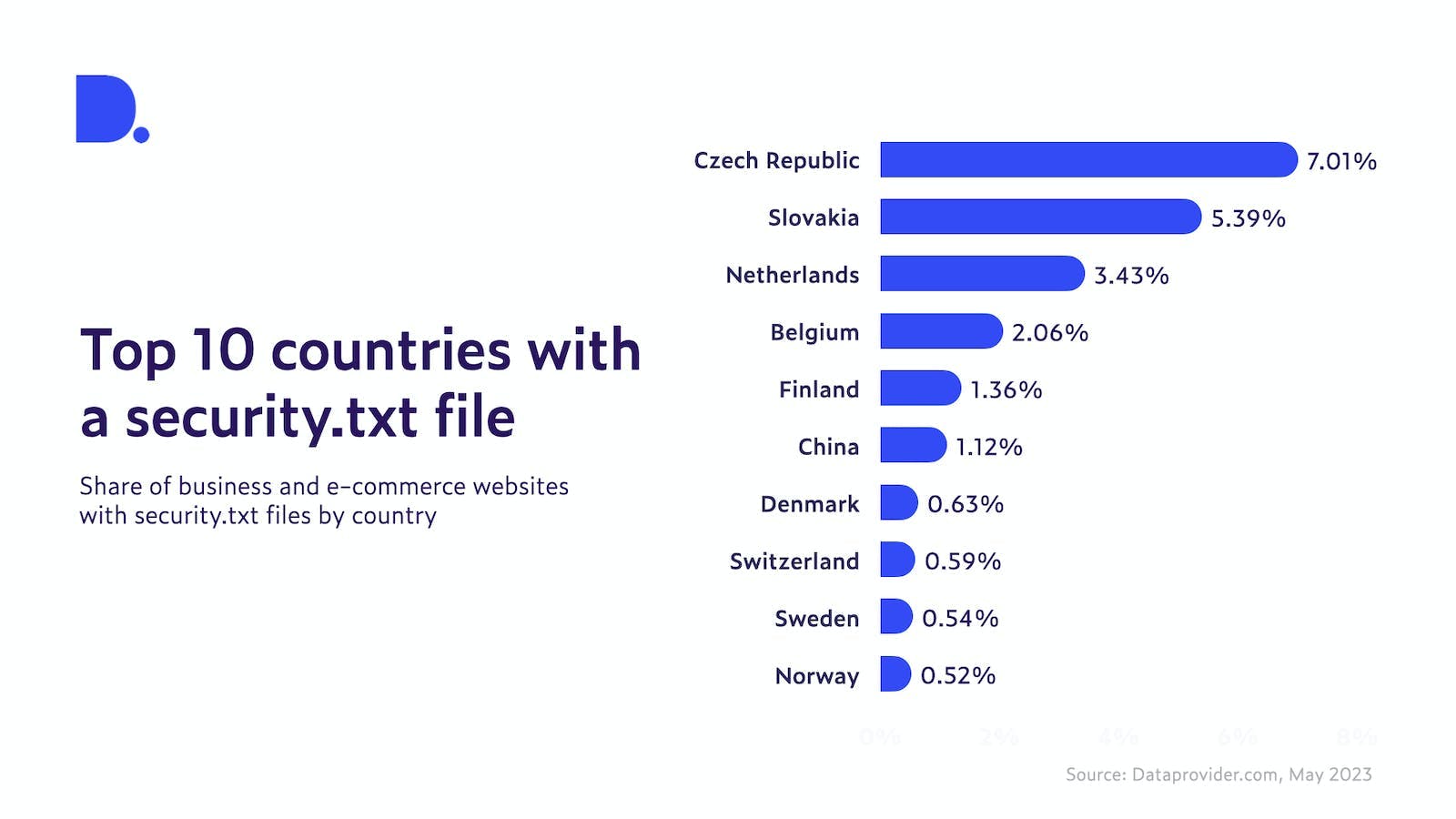
If we look at which country has the largest share of business and e-commerce websites with an implemented security.txt file, the Czech Republic and Slovakia have the largest share with 7% and 5% respectively. Except for China, the top 10 are composed entirely of European countries, with a strong presence of all four Nordic countries. Overall however, these percentages are rather small, meaning that all countries could do better at implementing policies to encourage businesses to adopt security.txt.
Security.txt enables businesses to take charge of their cybersecurity narrative. By directing researchers to the proper reporting channels, businesses prevent the potential chaos that may ensue if vulnerabilities were publicly disclosed without giving the organization a chance to fix them. By being proactive with a security.txt file, businesses can control the disclosure process. Doing this, they ensure they're part of the solution rather than just recipients of bad news.
While security.txt is not a silver bullet solution, it is indeed a significant first step in establishing a responsible vulnerability disclosure process. Let's understand why.
Security.txt lists the right contact information for security issues
The file provides a straightforward method for security researchers to contact the correct people about potential security risks. They often spend as much time trying to report the vulnerability as they do finding it, which is a deterrent for many. With the security.txt file, the process becomes easier, incentivizing more researchers to proactively report threats.
Implementing security.txt is relatively straightforward. The file should be placed under the /.well-known/ directory, making it accessible via https://[yourwebsite]/.well-known/security.txt. The information usually contained in this file includes contact details, typically an email, a link to a public key for securely communicating with the organization, and a link to the organization's security policy (Figure 3).
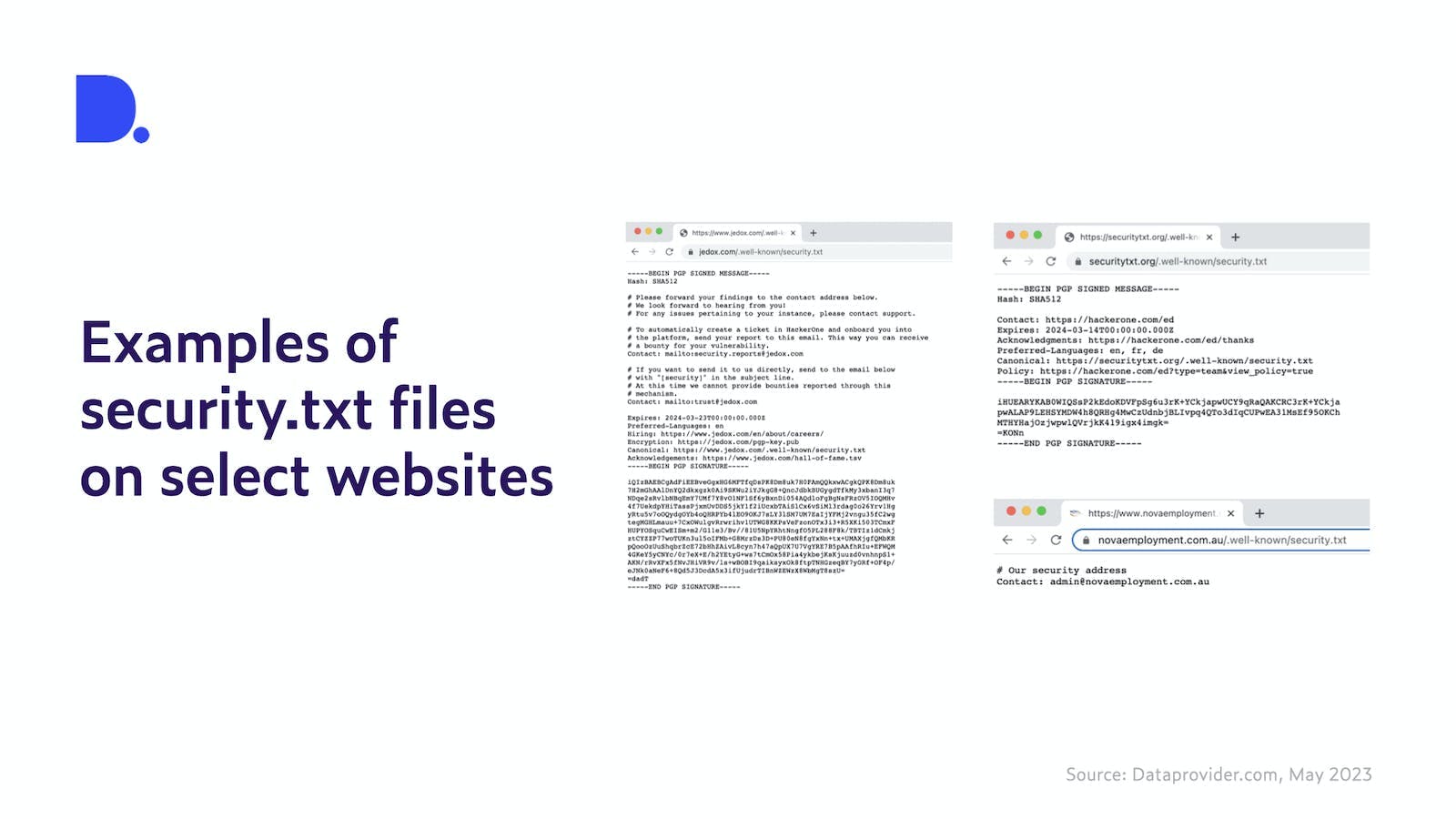
There are a few important points to consider when creating a security.txt file. It is important to ensure the contact details are up-to-date and accurate, for incorrect or obsolete information defeats the purpose of the file. Including a public key enables researchers to send sensitive information securely, while a link to the security policy helps researchers to understand your organization's stance and practices concerning security.
The first step in solving a problem is acknowledging it. By implementing a security.txt file, businesses not only acknowledge potential vulnerabilities in their systems but also take an active role in mitigating them. Despite its ease of implementation and clear benefits, it remains underutilized. Policy makers, domain registries and registrars as well as local website administrators can all help to raise awareness and promote the use of security.txt for creating a safer, more secure web for all.